Security
Data Security: encoding, encryption, hashing
#datasecurity #cybersecurity #security #encoding #encryption #hashing
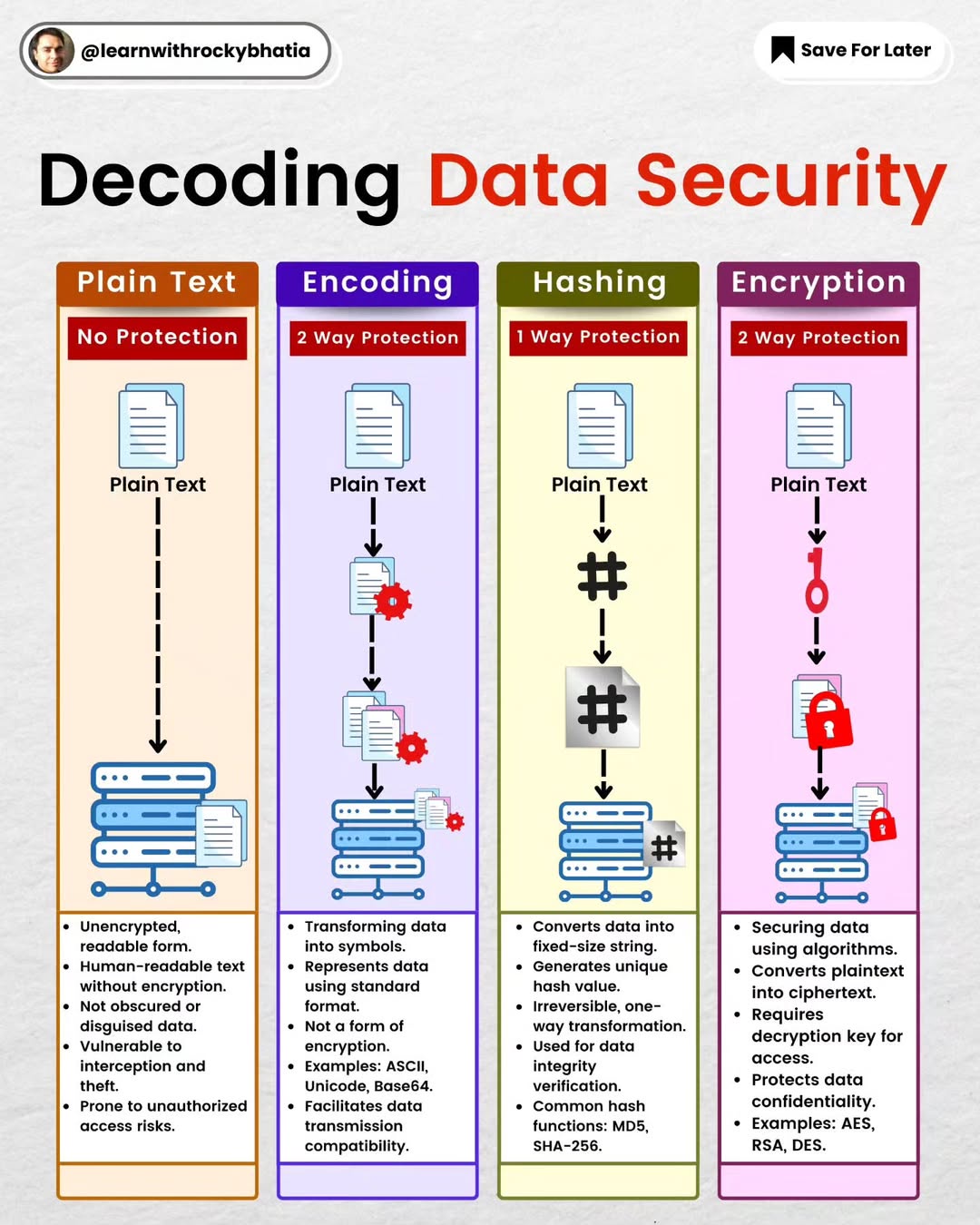
Have you ever found yourself scratching your head trying to figure out the differences between encoding, encryption, and hashing? Well, you're not alone. Let me break it down for you, minus the heavy tech lingo.
Encoding: Your Data's Passport
Think of encoding like giving your data a passport to travel internationally. It's all about converting data into a format that can be easily shared across different systems without confusion. Whether it's Base64, ASCII, or Unicode, encoding ensures that your message arrives intact, no matter where it's headed. Remember, encoding isn't about keeping secrets; it's about making sure your data can be understood anywhere and by anyone it's meant for.
Encryption: The Secret Agent
Now, if encoding is your data's passport, encryption is its secret agent disguise. When you encrypt data, you're scrambling it into a code that only someone with the right key can crack. It's the ultimate protection for your sensitive information, ensuring that only the intended recipient can see your message in its true form. Whether you're sending credit card info, private messages, or sensitive documents, encryption keeps your secrets safe from prying eyes.
Hashing: The One-Way Mirror
Hashing is a bit like a one-way mirror. It transforms your data into a fixed-size string or a “fingerprint,” but here's the kicker: you can't reverse the process. It's fantastic for checking if data has been tampered with or keeping passwords secure. If the data changes even a little bit, the hash will be completely different. It's a one-way trip – once your data is hashed, there's no going back.
Why This Matters to You Grasping these concepts is key in our digital age, especially if you're dabbling in digital communications, cybersecurity, or just want to keep your online presence safe. Each of these processes has its role, whether it's ensuring your data can travel safely, keeping your information private, or verifying that what you're seeing hasn't been messed with.
12 Essential Programmer Concepts
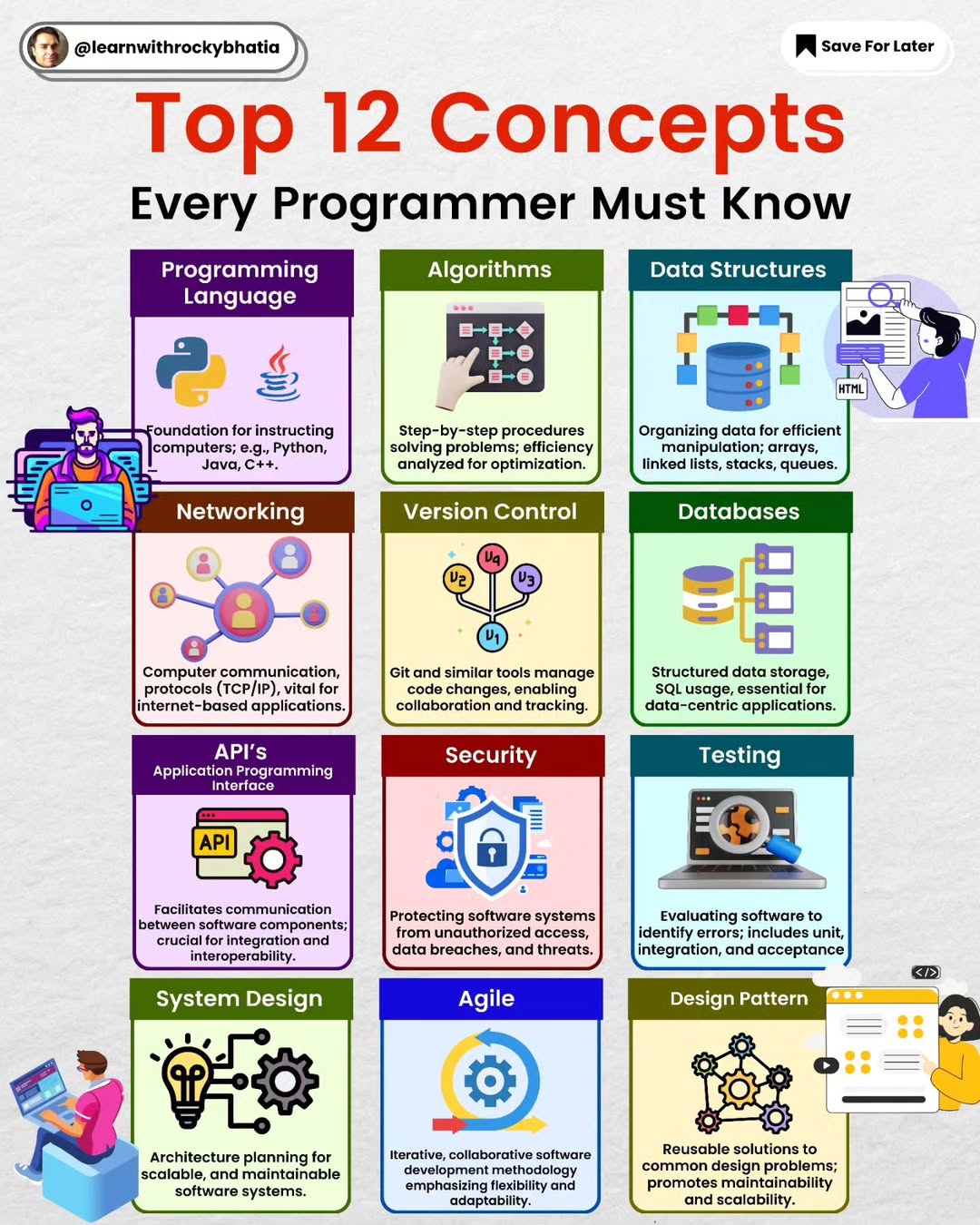
#programmingconcepts #systemdesign #security #coding #datastructures #algorithms #networking #versioncontrol #git #databases #api #agile
These comprehensive set of concepts forms a strong foundation for programmers, covering a range of skills from programming fundamentals to system design and security considerations.
1. Introduction to Programming Languages: A foundational understanding of at least one programming language (e.g., Python, Java, C++), enabling the ability to comprehend and switch between languages as needed.
2. Data Structures Mastery: Proficiency in fundamental data structures such as arrays, linked lists, stacks, queues, trees, and graphs, essential for effective algorithmic problem solving.
3. Algorithms Proficiency: Familiarity with common algorithms and problem solving techniques, including sorting, searching, and dynamic programming, to optimise code efficiency. ** 4. Database Systems Knowledge:** Understanding of database systems, covering relational databases (e.g., SQL) and NoSQL databases (e.g., MongoDB), crucial for efficient data storage and retrieval.
5. Version Control Mastery: Proficiency with version control systems like Git, encompassing skills in branching, merging, and collaboration workflows for effective team development.
6. Agile Methodology Understanding: Knowledge of the Agile Software Development Life Cycle (Agile SDLC) principles, emphasizing iterative development, Scrum, and Kanban for adaptable project management.
7. Web Development Basics (Networking): Fundamental understanding of networking concepts, including protocols, IP addressing, and HTTP, essential for web development and communication between systems.
8. APIs (Application Programming Interfaces) Expertise: Understanding how to use and create APIs, critical for integrating different software systems and enabling seamless communication between applications.
9. Testing and Debugging Skills: Proficiency in testing methodologies, unit testing, and debugging techniques to ensure code quality and identify and fix errors effectively.
10. Design Patterns Familiarity: Knowledge of common design patterns in object-oriented programming, aiding in solving recurring design problems and enhancing code maintainability.
11. System Design Principles: Understanding of system design, including architectural patterns, scalability, and reliability, to create robust and efficient software systems.
12. Security Awareness: Fundamental knowledge of security principles, including encryption, authentication, and best practices for securing applications and data.
Other areas could be OS, containers, concurrency and parallelism , basic web development etc.
API Security
Elevate Your Security Game: 20 Tips for Robust API Protection!
Embrace HTTPS: Secure data in transit by using HTTPS to encrypt communication between clients and your API.
OAuth 2.0: Implement OAuth 2.0 for robust authentication and authorization, ensuring only authorized users access your API.
WebAuthn: Enhance security with WebAuthn, a cutting-edge standard for passwordless authentication.
Fine-tuned Authorization: Create precise authorization mechanisms to control user access levels and protect sensitive resources.
API Key Usage: Improve your security with API keys, controlling access and monitoring usage effectively.
Rate Limiting: Implement rate limiting to prevent abuse and ensure fair usage, safeguarding your API from malicious attacks.
API Versioning: Future-proof your API by incorporating versioning, allowing for smooth transitions and backward compatibility.
Allow List Configuration: Strengthen security by configuring allow lists, specifying trusted entities, and minimizing potential risks.
API Gateway Deployment: Route your API traffic through a gateway for centralized control, security, and streamlined management.
Error Handling Mastery: Safeguard sensitive information by mastering error handling, providing meaningful responses without revealing internal details.
Bulletproof Input Validation: Fortify your API against injection attacks by implementing thorough input validation.
OWASP API Security Checklist: Regularly check your API against the OWASP API Security Checklist to ensure compliance with industry best practices.
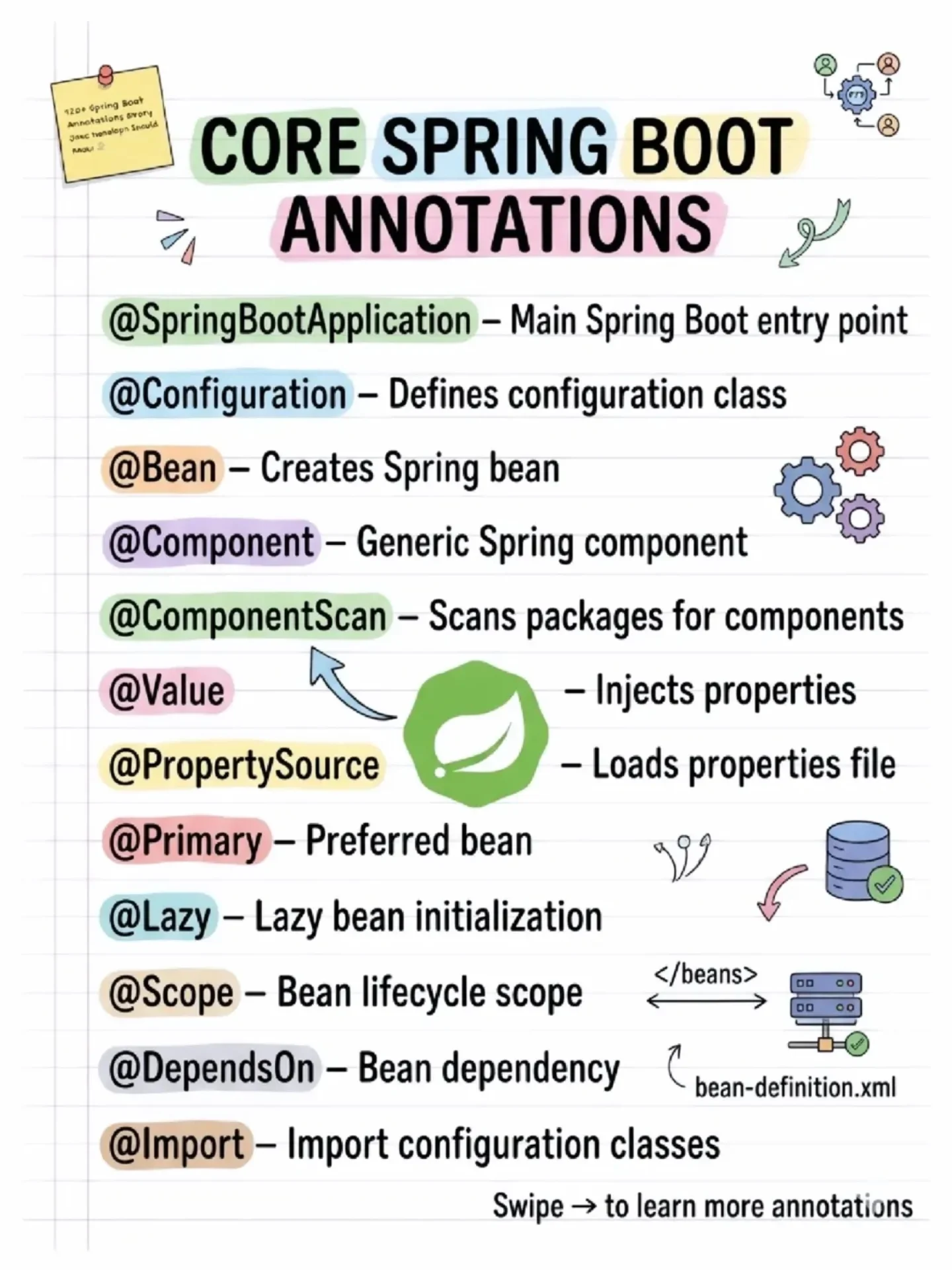
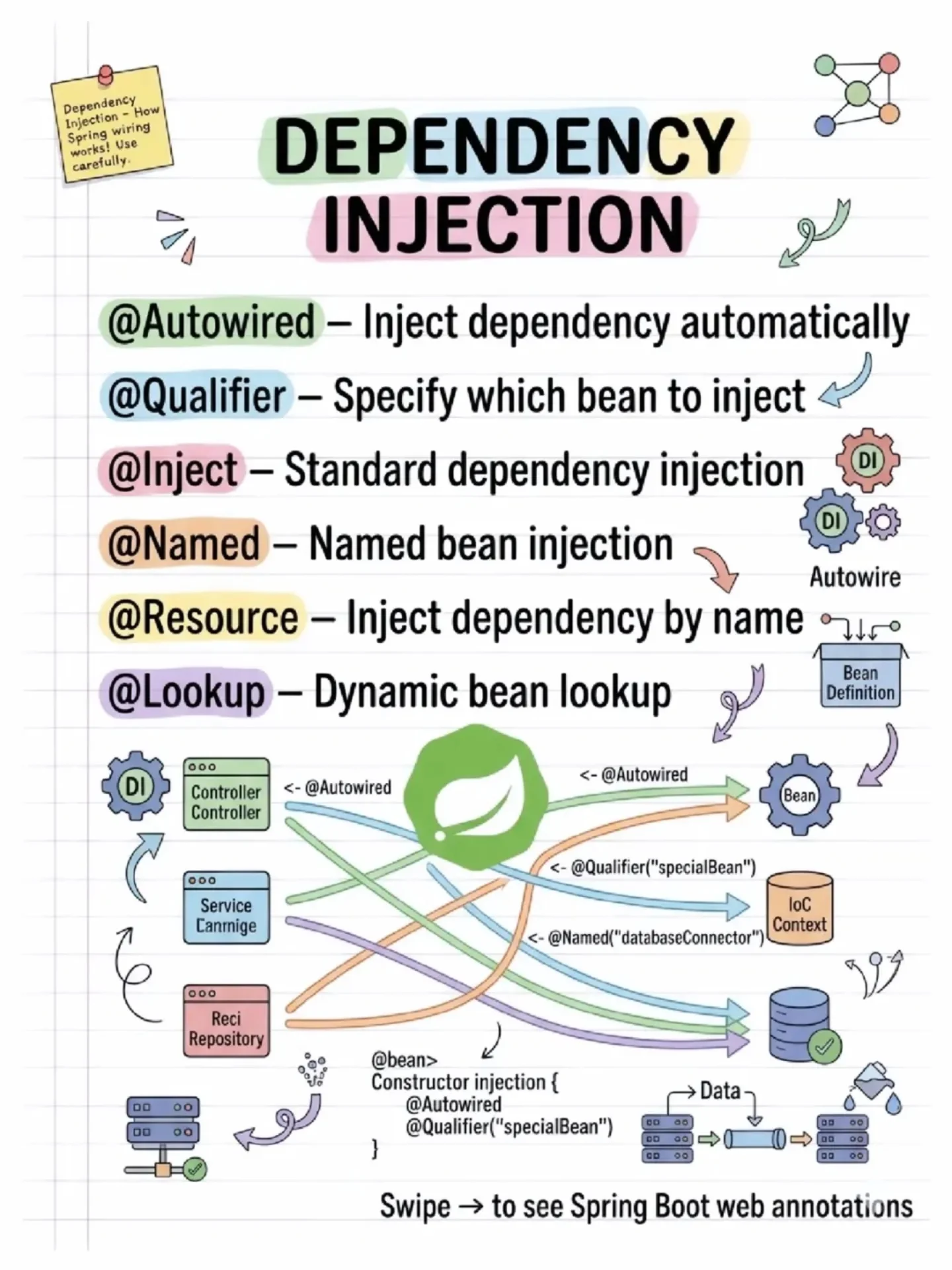
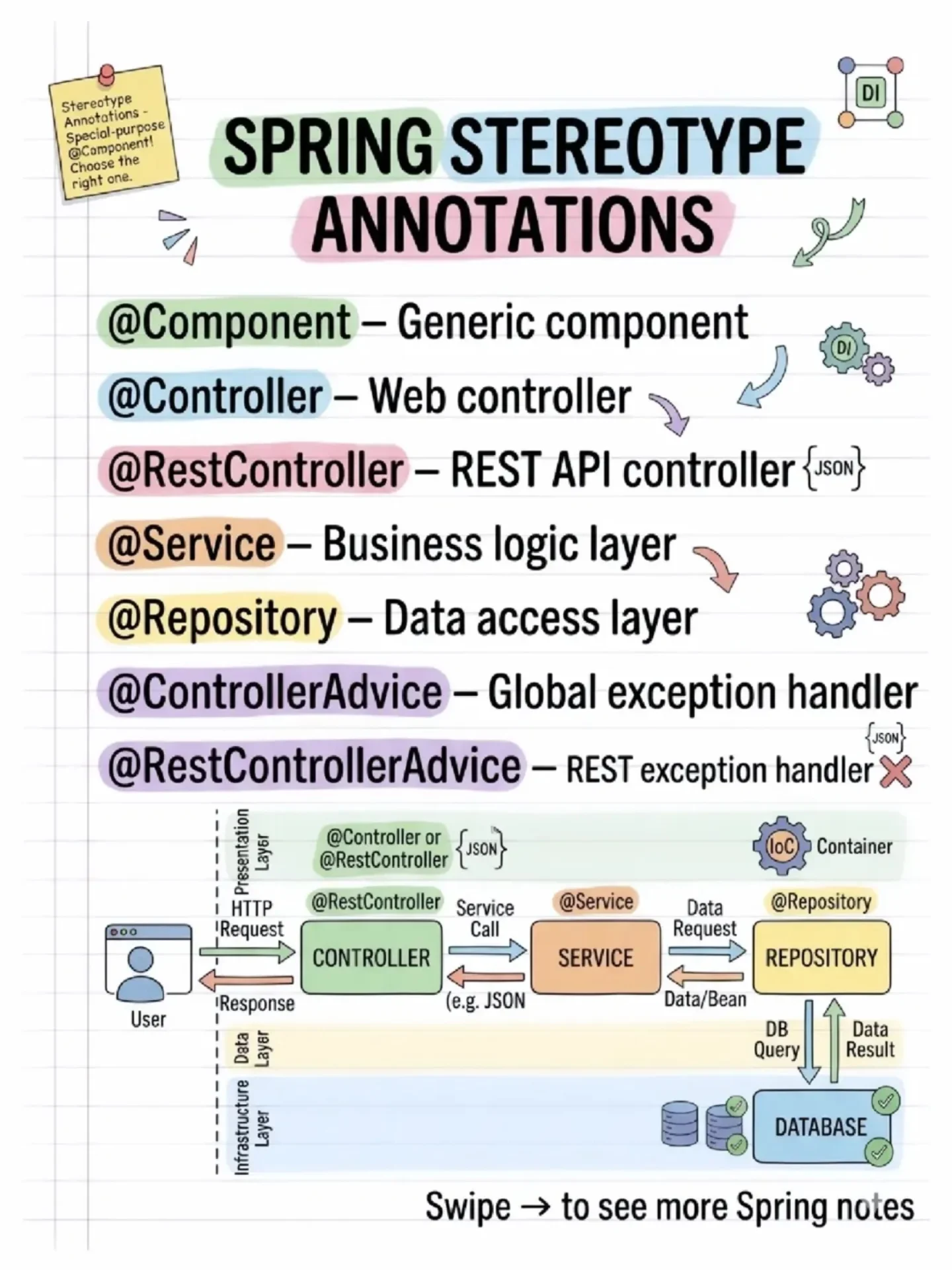
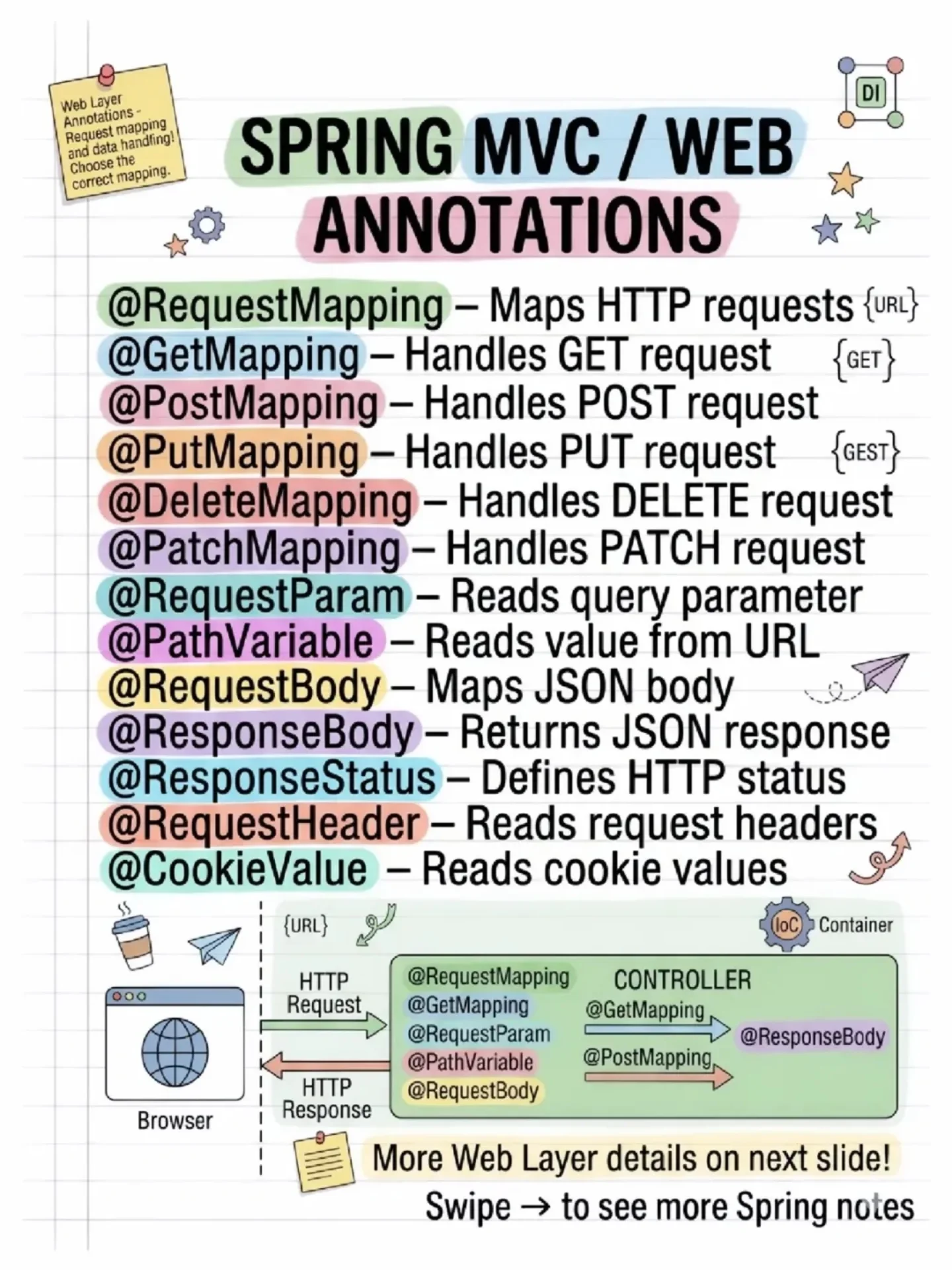
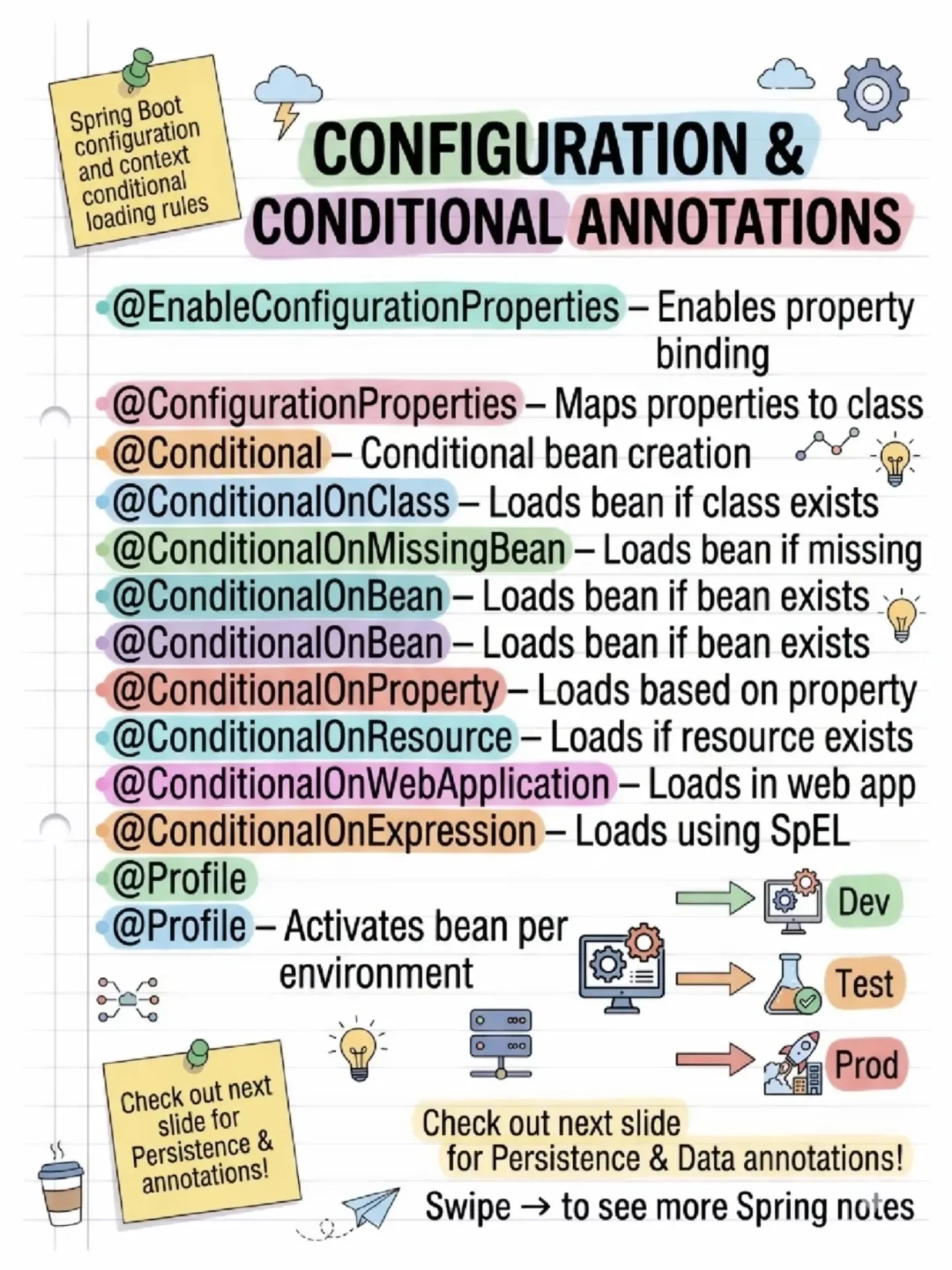
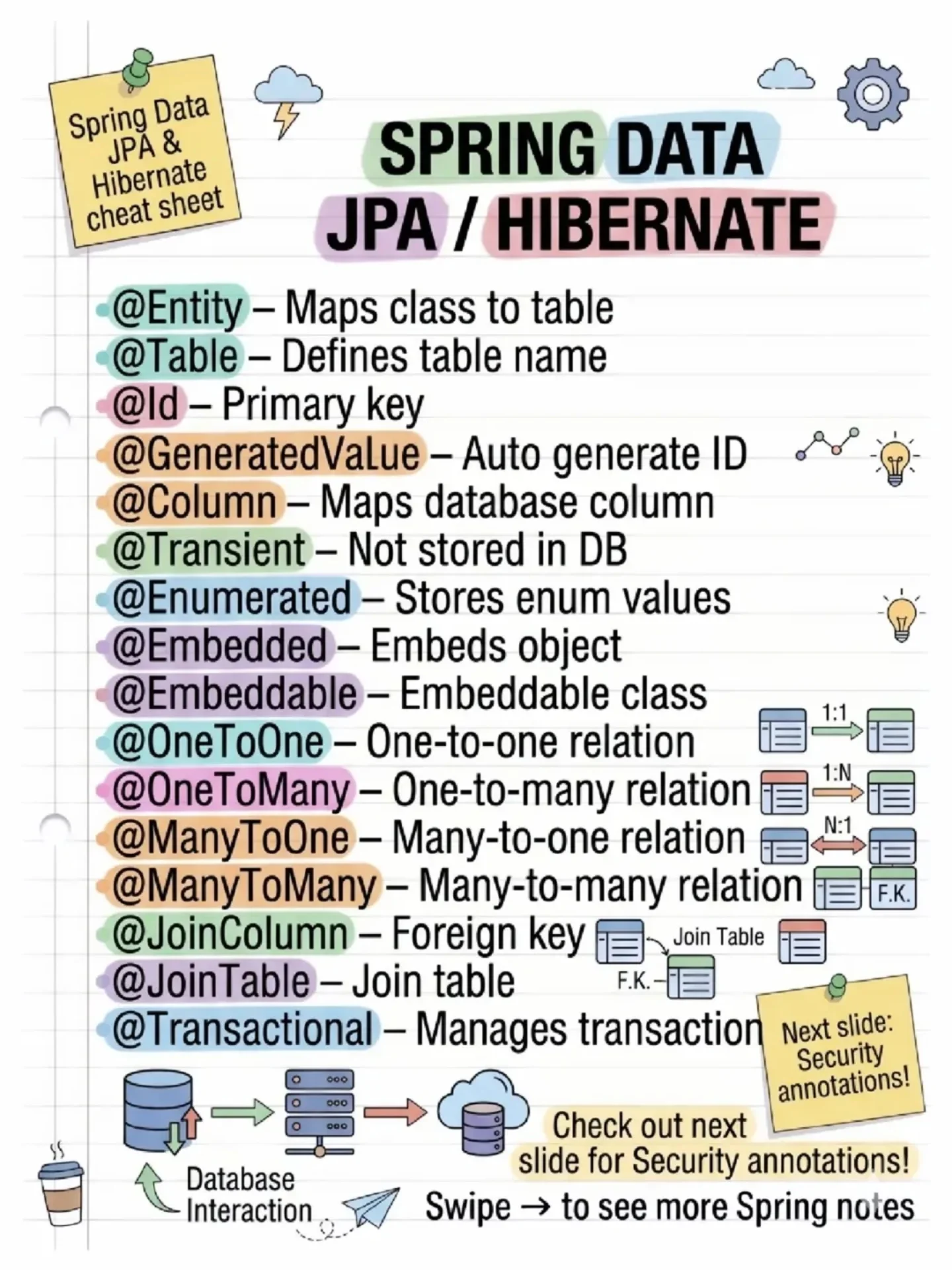
Spring Boot Annotations
API Security
API Roadmap
Secure APIs
Spring Security Architecture Explained
In today's world of rapidly evolving cybersecurity threats, protecting your application from unauthorized access is paramount.
Spring Security, a powerful and flexible framework, plays a critical role in securing Spring Boot applications.
Whether you're dealing with traditional username/password authentication, JWT tokens, or other custom mechanisms, Spring Security provides the necessary tools to handle authentication and authorization seamlessly.
In this blog, we'll dive into the Spring Security architecture, exploring how various components like the Security Filter Chain, AuthenticationManager, and Authentication Providers work together to secure your application.

1. Client Request
- A user or client makes a request to the application, usually to access a protected resource.
- This request is processed by a chain of Security Filters.
2. Security Filter Chain
- Security Filter A, B, ... N: These are different filters that apply to the incoming request, where each filter can handle specific types of security logic (like CORS, CSRF protection, and more).
- One of these filters is responsible for authenticating the user.
3. Authentication Flow
- UsernamePassword Authentication Token: This token represents the user's credentials (username and password) and is passed to the authentication logic.
- The authentication logic checks if the user credentials are valid. This typically involves checking a database or other identity source.
4. AuthenticationManager / ProviderManager
- The AuthenticationManager or ProviderManager manages the overall authentication process. It delegates the authentication request to different Authentication Providers based on the type of authentication required.
5. Authentication Providers
- JWTAuthentication Provider: If you're using JWT (JSON Web Token) for authentication, this provider handles the verification of JWT tokens.
- DaoAuthentication Provider: This provider handles traditional authentication using a database, checking user credentials against stored data (e.g., in a relational database).
- Other Providers (Authentication Provider N): You can define multiple custom authentication providers if your application supports multiple methods of authentication (e.g., OAuth2, LDAP).
6. UserDetailsService
- The UserDetailsService is responsible for loading user-specific data, typically by looking up the user’s details from a database (using the DaoAuthenticationProvider).
- The PasswordEncoder ensures that passwords are securely encoded (hashed) before they are compared during the authentication process.
7. SecurityContext & JWT Authentication Filter
- If the user is successfully authenticated, the SecurityContext is updated to store the user’s authentication status.
- The JWT Authentication Filter is responsible for handling JWT tokens, ensuring that valid tokens allow access to protected resources.
8. Authentication Request/Response
- Once the authentication is performed by the filters and providers, an Authentication Request is sent to the backend.
- After validation, an Authentication Response is returned, which could contain the authentication token (such as a JWT), allowing the client to access secure resources in subsequent requests.
9. SecurityContextHeader
- The SecurityContextHeader encapsulates important security information like the user’s Principal (authenticated user), Credentials (such as the password or token), and Authorities (permissions or roles).
- These fields include:
getAuthorities(): Fetches the roles or permissions granted to the user.getPassword(),getUsername(): Standard user details.isAccountNonExpired(),isAccountNonLocked(),isCredentialsNonExpired(),isEnabled(): These are checks to ensure the user account is in good standing (not expired, locked, etc.).